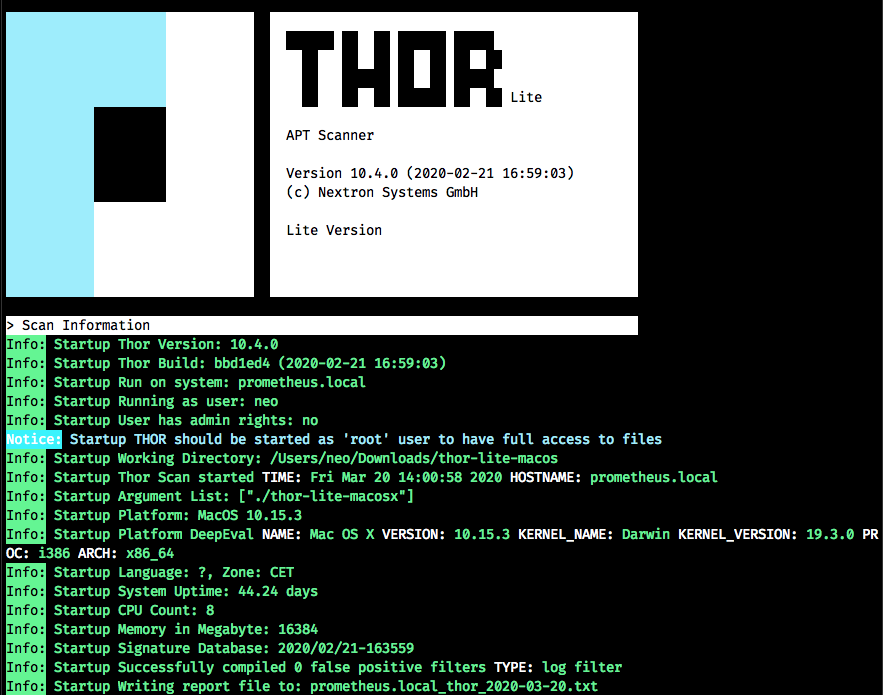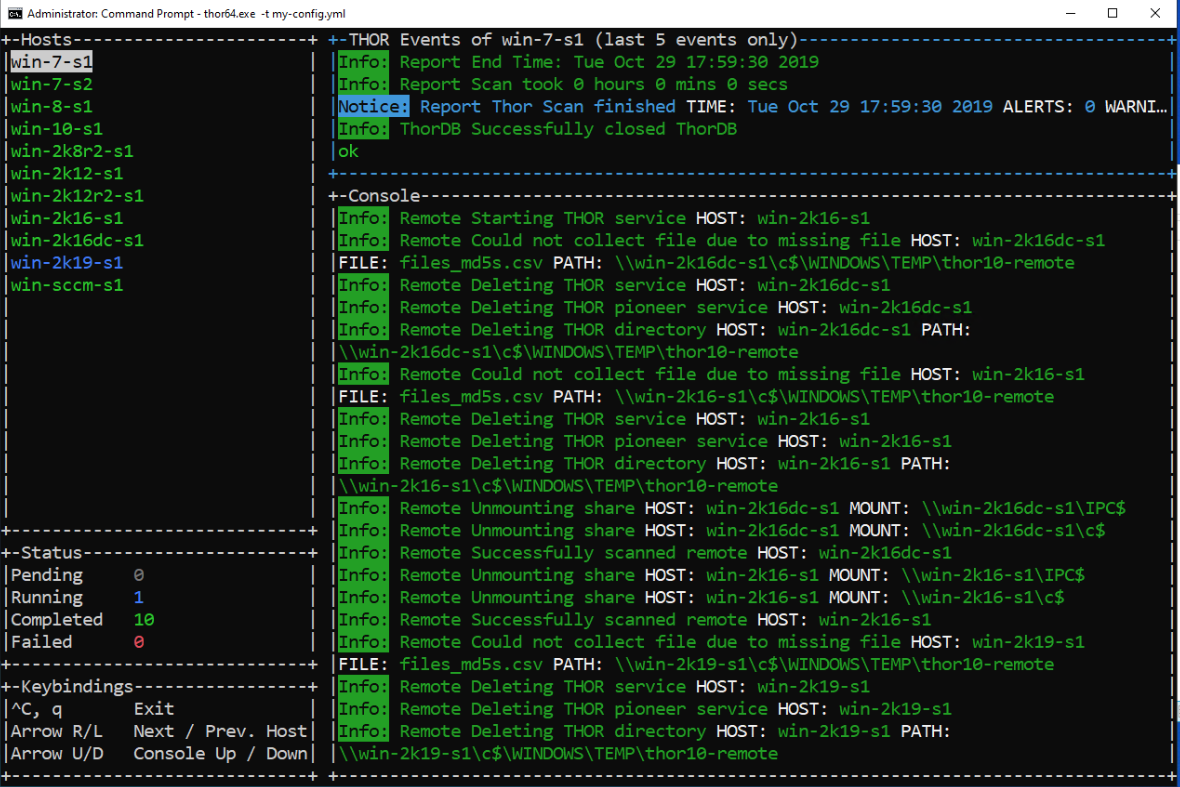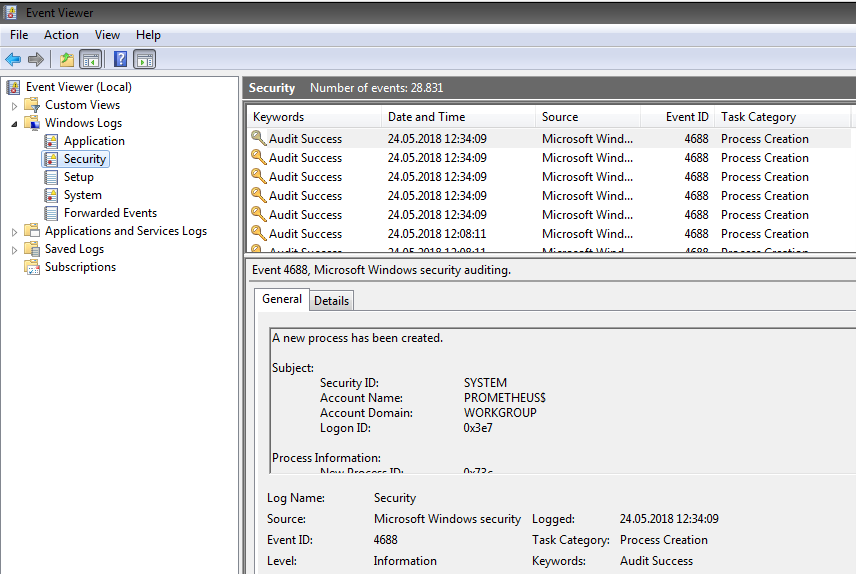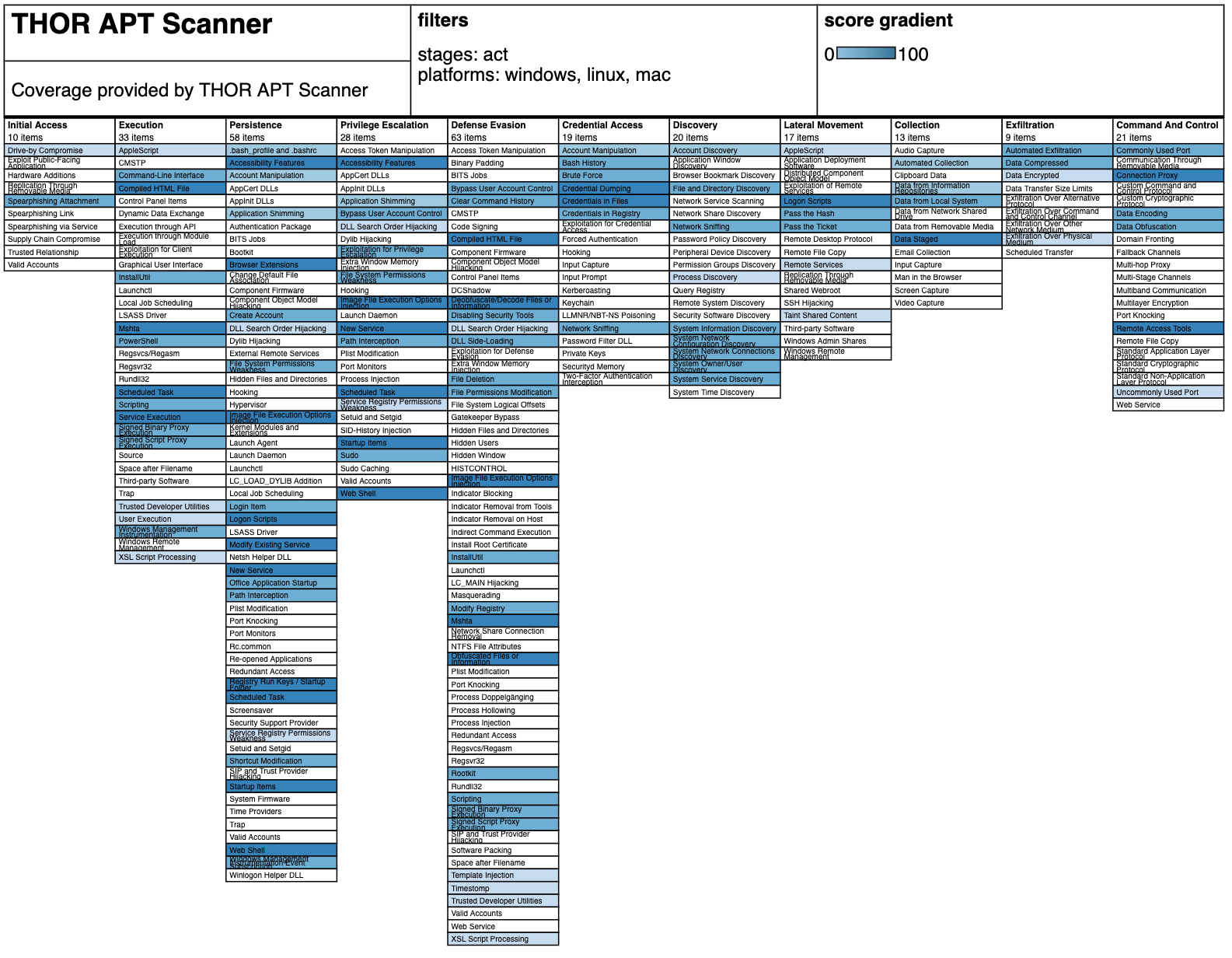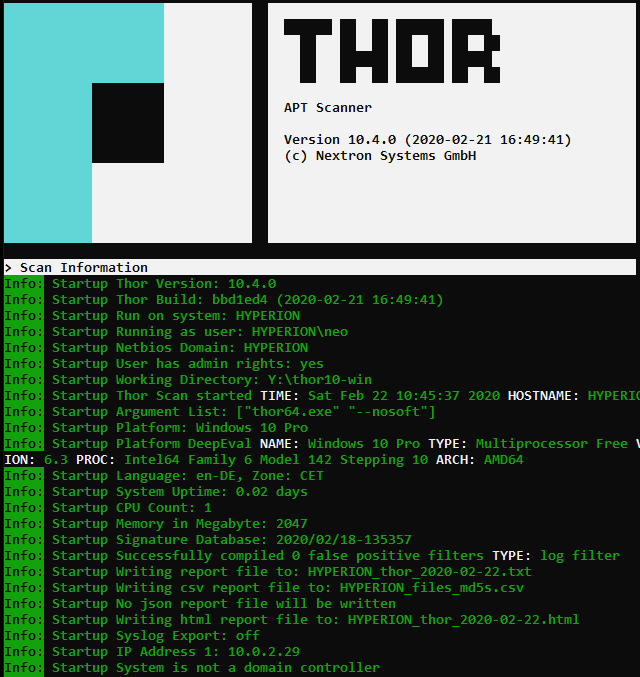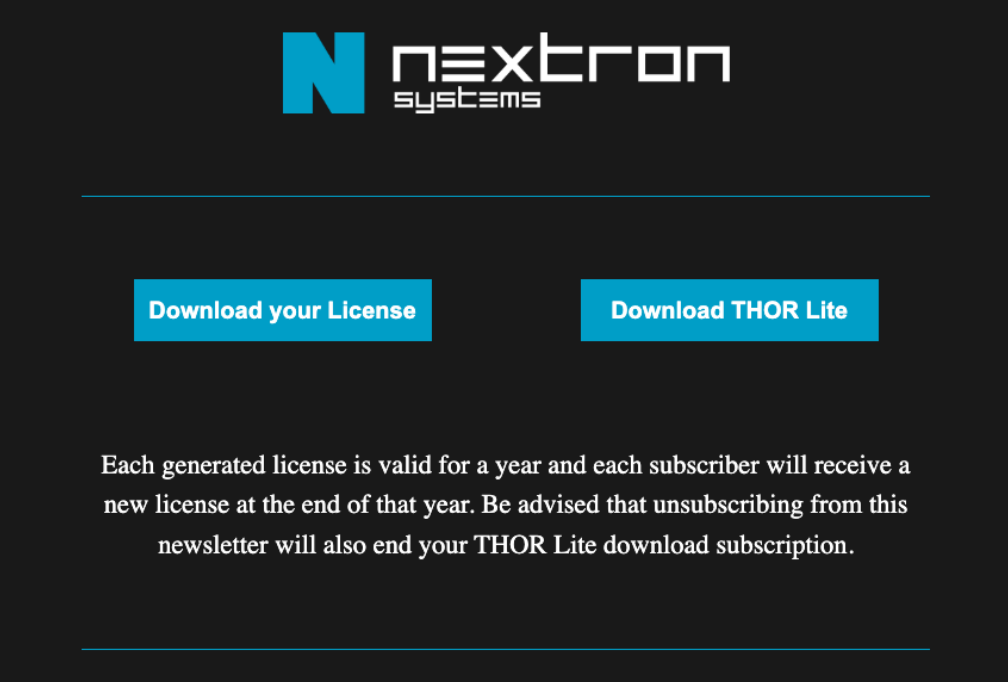
How to scan systems with THOR lite scanner during compromise assessment and incident response | by Md. Mahim Bin Firoj | Sep, 2023 | Medium

How to scan systems with THOR lite scanner during compromise assessment and incident response | by Md. Mahim Bin Firoj | Sep, 2023 | Medium